Cybersecurity is changing faster than ever. One recent incident shows just how quickly threats can turn into real attacks. A vulnerability known as CVE-2026-39987 was exploited in less than 10 hours after it was publicly disclosed.
This happened in a tool called Marimo, a platform used by developers and data scientists. The speed of this attack highlights a serious shift in how cyber threats work today.
What Happened in Simple Terms
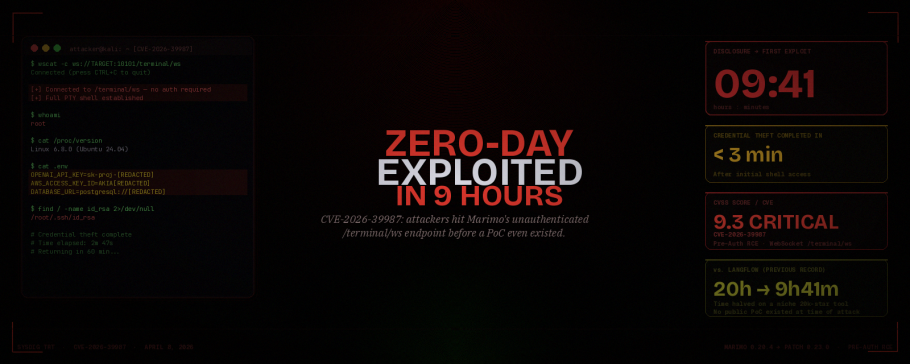
On April 8, 2026, a critical flaw in Marimo was made public. This flaw allowed attackers to access a system without needing a password. Within just 9 hours and 41 minutes, someone had already used it to break into a system.
Once inside, the attacker was able to:
- Access sensitive files
- Steal API keys
- Retrieve cloud credentials
- Extract SSH access details
Even more concerning, the attacker completed the main data theft in under three minutes.
Why Marimo Was an Easy Target
Marimo is not a massive enterprise platform, but it is widely used by developers and researchers. These environments often store valuable data such as:
- API keys for AI services
- Cloud access credentials
- Database login details
- Private SSH keys
When an attacker gains access to such a system, they do not just compromise one machine. They potentially gain access to entire cloud environments and connected services.
What Was the Actual Problem
The issue came from a small but critical mistake in the system.
One part of Marimo required authentication before access. Another part, specifically a terminal feature, did not check for authentication at all.
This meant that anyone who could connect to the system could open a terminal and run commands freely, just like having full access to a computer.
This kind of vulnerability is known as a remote code execution flaw, one of the most dangerous types in cybersecurity.
Why the Attack Happened So Fast
In the past, attackers needed time to understand a vulnerability and build an exploit. That is no longer the case.
Today, attackers can:
- Monitor vulnerability announcements in real time
- Use AI tools to generate exploit code quickly
- Test and launch attacks within hours
Even though no public exploit code was shared for this vulnerability, the attacker was able to create one using just the description.
This shows how advanced and efficient modern cyber threats have become.
A Growing Trend in Cybersecurity
This incident is not isolated. The time between vulnerability disclosure and exploitation has been shrinking rapidly.
- In 2018, it took years for many vulnerabilities to be exploited
- By 2024, it dropped to a few hours
- In 2026, it is now happening within the same day
This means there is almost no safe window between discovering a problem and being attacked.
What This Means for Businesses
For companies and developers, this is a serious warning.
You can no longer wait days or weeks to fix critical issues. Immediate action is now essential.
Here are some key lessons:
1. Patch Immediately
As soon as a critical update is released, it must be applied without delay.
2. Avoid Public Exposure
Tools like Marimo should not be directly accessible on the internet without protection.
3. Protect Sensitive Data
Store API keys and credentials securely, not in easily accessible files.
4. Monitor Systems Continuously
Keep track of unusual activity, especially after a vulnerability is disclosed.
5. Assume Breach When in Doubt
If a system is exposed, assume it has been compromised and rotate all credentials.
The Bigger Shift: AI and Faster Attacks
One major factor behind this speed is artificial intelligence.
AI tools can now analyze vulnerability descriptions and generate working attack methods in seconds. This gives attackers a huge advantage and reduces the time needed to act.
This also means defenders must use AI and automation to keep up.
Final Thoughts
The Marimo vulnerability is a clear example of how cybersecurity has changed. The time between discovery and attack is now extremely short.
For businesses, this means moving from reactive security to real-time defense. Waiting is no longer an option.
The future of cybersecurity will depend on speed, automation, and constant vigilance.